NSX vSphere Distributed Firewall and the 80/20 Rule…
A little clarification about the NSX vSphere Distributed Firewall together with 3rd party partner integration… First, NSX as an ecosystem platform and provides extensibility to allow 3rd party partners to interoperate between NSX and their respective technology solutions….
One of the integration points available with NSX is integration with the NSX vSphere hypervisor based distributed firewall together with a parter firewall management system. As an example of this is the fine integration with Palo Alto Network’s (PAN) Panorama centralized UI together with the NSX vSphere Distributed Firewall which allows customers to manage firewall policy across PAN physical firewalls, PAN virtual firewall appliances, and the NSX vSPhere Distributed Firewall.
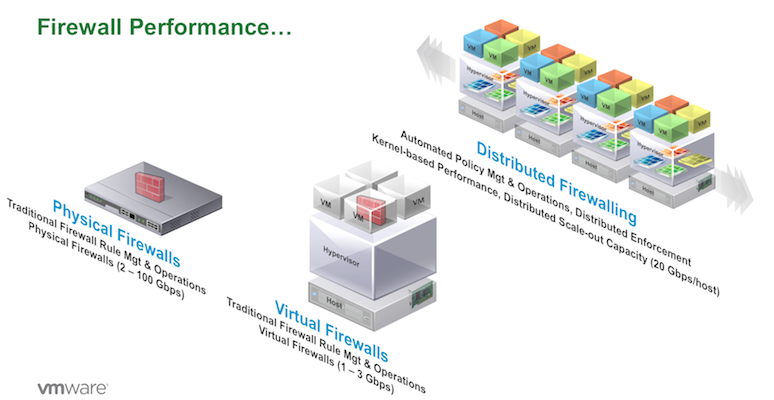
The ideal would be that every single network byte travels through a physical or virtual firewall, and wonderful Next Generation Firewall (NGFW) capabilities occur associated with advanced traffic analysis and security policy execution… Today that’s impossible!
A NGFW physical firewall appliance can manage up to around 100Gbs and a virtual NGFW appliance can manage up to around 2-5Gbps. Given multi Gbps streams generated by VM’s within the Hypervisor, the only way to provide high performance firewall processing is to extend firewall capabilities into the hypervisor itself – This is what VMware has done with the NSX vSphere Distributed Firewall providing firewall processing at up to 20Gbps per hypervisor.
To be clear, the NSX Distributed Firewall is not a NGFW, but it is a very good Layer 4 stateful firewall which has the following five major features:
- Policy can be based on vSphere, VM, and security tag constructs as well as traditional IP constructs.
- Policy can be dynamic. As an example, updating a VM with a new or changed security tag will automatically inherent security policy associated with the security tag. Set a security tag on a VM with DB=MYSQL, and predefined security policy associated with MYSQL is dynamically applied.
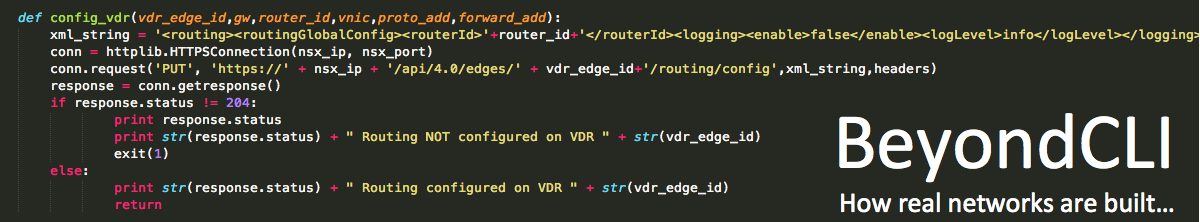
- Policy can be created via the RESTful API as part of an orchestration workflow.
- Its fast – the vSphere Distributed Firewall supports 20Gbps per Hypervisor so as you scale up the numbers of hypervisors in your environment, you also also scaling the amount of bandwidth/performance associated with distributed firewall processing.
- Firewall policy is being applied on the vNIC of every VM irrespective of the network topology of the VM’s. If all the VM’s are on the same network, distributed firewall policy can still isolate flows as appropriate between the VM’s… Pretty awesome!
So the 80/20 rule for the NSX vSphere Distributed Firewall is this….
- Use your favorite NGFW UI if you like.
- Create FW rules based on NGFW Policy, IP Sets, and/or vSphere/VM constructs such as VM name or VM Security Tags.
- Let the NSX vSphere Distributed Firewall do the “heavy lifting” with L4 stateful firewall rules – The 80%
- Let NSX “Traffic Steer” to your favorite NGFW Virtual Appliance to perform the sweet NGFW magic on the flows that really need it – The 20% 😉